GP.Identity+Permission Management
| Page maturity This page has maturity level 3 (usable) |
| GP | Identity & Permission Management | Version: | 0.5 | 
| |
|---|---|---|---|---|---|
| Document type: | Generic Pattern | Owner: |
| Instances of this Generic Pattern are able to maintains the propagation and consistency of digital identities and digital permissions that are recognized within the organization. |
Description
This Generic Pattern belongs to "Operations". Instances of this Generic Pattern are able to maintains the propagation and consistency of digital identities and digital permissions that are recognized within the organization.
Identity management This Generic Pattern can perform the following tasks related to digital identities:
- It can provide new digital identities to instances of A&A services when the circumstances call for it (either an eligible new identity presents itself in another connected A&A system that's deemed authoritative, or an existing identity becomes eligible), including all accompanying identity attributes that are used in that particular A&A service instance;
- It can provide new digital groups to instances of A&A services that are going to be involved with Role Based Access Control under that A&A service's authority;
- It can direct A&A services to change group membership of a digital identity to reflect a change in roles;
- It can convey the effects of a change in business rules on the relevant aspects of the digital identities under an affected A&A service;
When an update occurs in a digital identity's attribute under an A&A service that's deemed authoritative for that attribute, then the Pattern can detect this update, and have it applied to all A&A services that contain that same identity and attribute;
- It can direct A&A services to disable or remove identities, as soon as that identity's eligibility for an account in that particular A&A service ends, or the digital identity is disabled or removed from an authoritative A&A service;
- It can automatically resolve certain conflicts in account information between different A&A services.
Permission management This Generic Pattern can perform the following tasks related to permission management:
- It can direct an A&A service to create or update the necessary permissions associated with a digital resource, when a digital identity becomes eligible for use of this resource;
- It directs an A&A service to update or remove the relevant permi rsions associated with a digital resource, when a digital identity loses eligibility for use of this resource;
- It can detect and resolve certain conflicts between specific permissions assigned (or not) to a digital identity by a specific A&A service, and the permissions that should (or should not) actually be granted to it
Services realized
This Pattern realizes the following service(s):
- Identity & Permission Management (This service maintains the propagation and consistency of digital identities and digital permissions that are recognized within the organization.)
Functional and Integration view
This is the graphic representation of the functional model of this Generic Pattern:
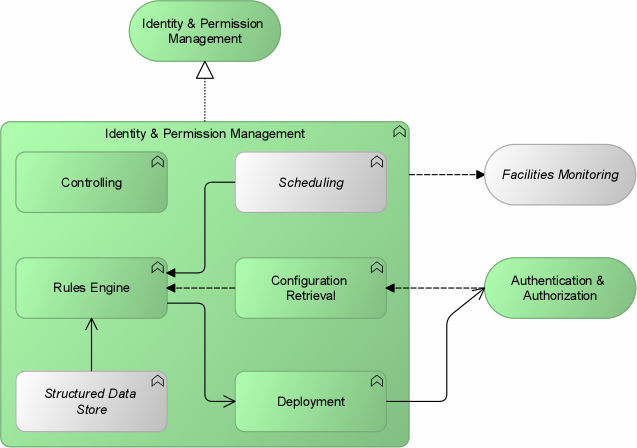
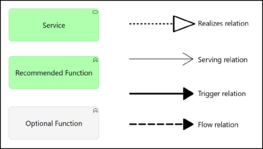
Generic Pattern Composition
This pattern is an aggregation of the following (mandatory and optional) functions, expressed in Generic Functions:
| Icon | Function | Inclusion | Rationale |
| Rules Engine | recommended | This function processes new or changed digital identities and/or permissions. It can source authoritative identity attributes and permissions from multiple connected A&A services. Furthermore, it hands off new or changed identity (attributes) and/or permissions to the Deploying function for replication over the relevant A&A services. | |
| Structured Data Store | optional | Unless the Pattern is implemented as a Virtual Metadirectory, the Pattern needs a means remember the state of the identities/permissions it has distributed over the organization; this function provides this means. Ideally the function contains a metadirectory combining the authoritative data of all appointed identity stores and permission registers (although it's most likely unwanted to have any facility call upon this metadirectory directly). If not a metadirectory, then still some sort of record needs to be kept to prevent the Pattern from unnecessarily provisioning accounts, or missing out on updated accounts. | |
| Configuration Retrieval | recommended | The Pattern needs a means to interrogate connected A&A services that receive data and/or supply (authoritative) data. Hence this function serves to model this means. Interrogation can occur on external triggers (a change in a monitored Store/Register), on schedule, or on another internal trigger. | |
| Scheduling | optional | This function serves to model the timed triggers that cause the Pattern to perform tasks such as collection or deployment of A&A information. | |
| Deploying | recommended | This function enables the Pattern to push the new or changed identity (attributes) and/or permissions to connected A&A services. | |
| Controlling | recommended | If implemented, this function can be used by administrators, and possibly by authorized clients, to change the way the Pattern works. Among the changes that can be made via this function are:
Care must be taken to limit access to this function to authorized systems and users. |
Services connected with this Generic Pattern
This Generic Pattern has the following mandatory and optional relations with adjacent Generic Services.
| Service | Adjacency | Summary | Rationale |
| Authentication & Authorization | recommended | This service can validate an identity claim, and it can validate the permissions required for an action, as part of an Authentication & Authorization process. | As this Pattern serves to consolidate multiple A&A services, they are required to be connected. |
| Facilities Monitoring | optional | This service allows its users to monitor IT facilities with the aim of guarding operational continuity or security. | Correct management of digital identities and permissions is vital to client's access to IT services, as well as to the security of the organization's IT resources. This calls for monitoring of this Pattern by both IT Operations staff and security officers. |
Applied Patterns based on this Generic Pattern
The following Applied Patterns are based wholly or in part on this Generic Pattern: