GP.Authentication+Authorization
| Page maturity This page has maturity level 3 (usable) |
| GP | Authentication & Authorization | Version: | 0.2 | 
| |
|---|---|---|---|---|---|
| Document type: | Generic Pattern | Owner: |
| Helps to secure IT facilities and applications by validating digital identities and permissions. |
Description
This Generic Pattern belongs to "Core". This Pattern helps to secure IT facilities and applications by validating digital identities and permissions. In effect, this Pattern carries out some of the automated parts of the Authentication and Authorization process - note that many steps in this process are not automated, but are carried out by human beings. Authentication is done when someone wants to make sure - to a certain extend - that a claim that a subject makes on a digital identity is true. A special form of authentication is identification, which is a check that finds a match between a subject and a digital identity. Authorization is the process of granting rights to a subject to use a certain resource; the exercising of these rights is then subject to validation, which can be carried out automatically.
When it comes down to the use of automated systems and data, a process is needed to check if someone is entitled to this use. This means that records are made of authorizations (permissions), that need to be validated if someone is issuing rights (Permission Validation). To identify a digital user as a real world person or system, the digital identity (a digital representation of the real world identity) claim is validated by means of comparing one or more credentials that are provided during the validation with credentials that were stored earlier when the digital identity was created and administered (e.g. password hashes, biometric hashes, tokens, certificates). Thus, the Identity Validation function is an automated rematch of the real identity with the digital identity of a user. The Permission Validation function is an automated check whether a user has the right permissions to use a certain resource or data
Further notices
It is a good practice to limit digital identities to natural persons and discrete systems. If this is the case, then the validation of such digital identities (and the logs thereof) has meaning in a legal context. This is of particular importance for the process of Auditing.
Services realized
This Pattern realizes the following service(s):
- Authentication & Authorization (This service can validate an identity claim, and it can validate the permissions required for an action, as part of an Authentication & Authorization process.)
Functional and Integration view
This is the graphic representation of the functional model of this Generic Pattern:

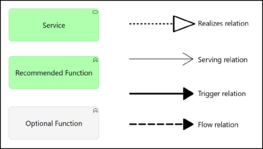
(The source file of this image can be downloaded here).
Generic Pattern Composition
This pattern is an aggregation of the following (mandatory and optional) functions, expressed in Generic Functions:
| Icon | Function | Inclusion | Rationale |
| Identity Store | recommended | This function is required because it offers the Identity Validation the data it needs to perform the validation. | |
| Identity Validation | recommended | This function delivers the functionality of validating a digital identity. | |
| Permission Register | recommended | This function provides Permission Validation with the ability to retrieve the current valid (set of) permissions. Note that the permissions themselves likely have a relation with a (particular) Identity Store, since many permissions are granted based on identity attributes like user ID, group membership or (for example) Job Title. | |
| Permission Validation | recommended | If authorization is needed, then this function will provide it. Note that it requires access to a Permission Register, but most likely also to an Identity Store, since many permissions are granted based on identity attributes like user ID, group membership or (for example) Job Title. | |
| Controlling | recommended | The purpose of this function within the Pattern is to focus the attention on the security aspects of an available means to read and/or alter the content of either the Identity Store or the Permission Register. |
Services connected with this Generic Pattern
This Generic Pattern has the following mandatory and optional relations with adjacent Generic Services.
| Service | Adjacency | Summary | Rationale |
| Data Transport | recommended | This service transports data between automated systems. | There are Data Transport instances used within the Pattern, between the Pattern and adjacent services, and between the Pattern and the consumers of its realized services. These must be secured sufficiently to guarantee the integrity of the Pattern and its operations. |
| Identity & Permission Management | optional | This service maintains the propagation and consistency of digital identities and digital permissions that are recognized within the organization. | To maintain the information in the Identity Store and Permission Register, the Identity & Permission Management Pattern is required. It provisions accounts, ensures information is kept correct and current, and makes auditing possible, both on granted permissions and on changes in identity and/or permission information itself. |
Applied Patterns based on this Generic Pattern
The following Applied Patterns are based wholly or in part on this Generic Pattern: